The Main Account is the root of the ARGLabs AWS Organization, but it is intentionally minimal. It does not run any workloads. Its only job is to host the pieces that have to live at the very top of the tree: the organization structure, the identity provider for everyone who logs into AWS, and the company’s main domain.
What it provisions
- AWS Organizations: a
TeamsOU (Cloud Team, App Team) and aSharedOU. - IAM Identity Center (SSO): a
CloudAdministratorsgroup, anAdministratorAccesspermission set, the account assignment that grants the group admin on the Main Account, and the group membership for the configured admin users. - Route 53: the
arglabs.orghosted zone and the registered domain entry, wired to that zone name servers.
How it deploys
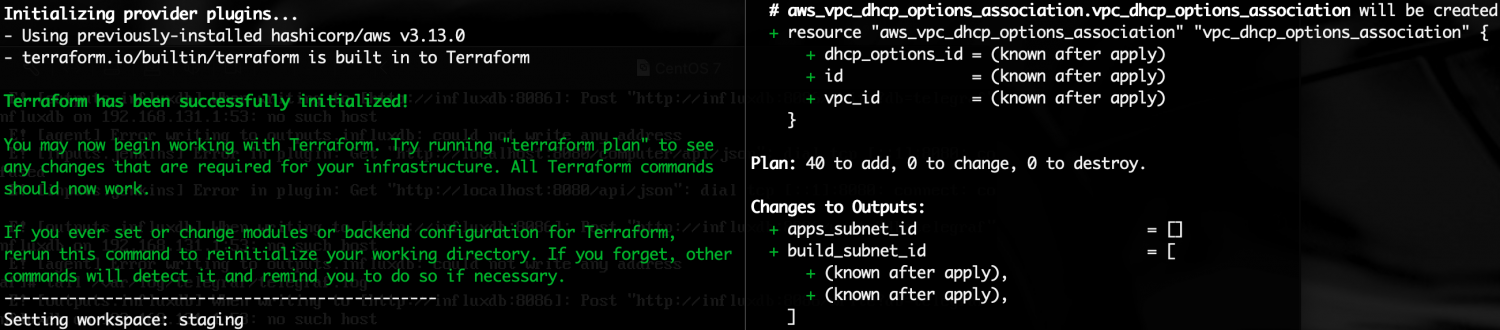
Everything runs through Bitbucket Pipelines. The pipeline assumes the bitbucket-openid role via OIDC (provisioned by the pre-requisites project), which in turn assumes the deployer role to actually touch AWS. No long-lived credentials anywhere.
The main branch pipeline runs terraform plan, an Infracost cost estimate, a “should we deploy today?” guard (no Friday deploys), and then waits for a manual approval before applying. There is also a gitops branch that short-circuits straight to apply for cases where you know what you are doing.
Repository: bitbucket.org/arglabs/arglabs-mainaccount